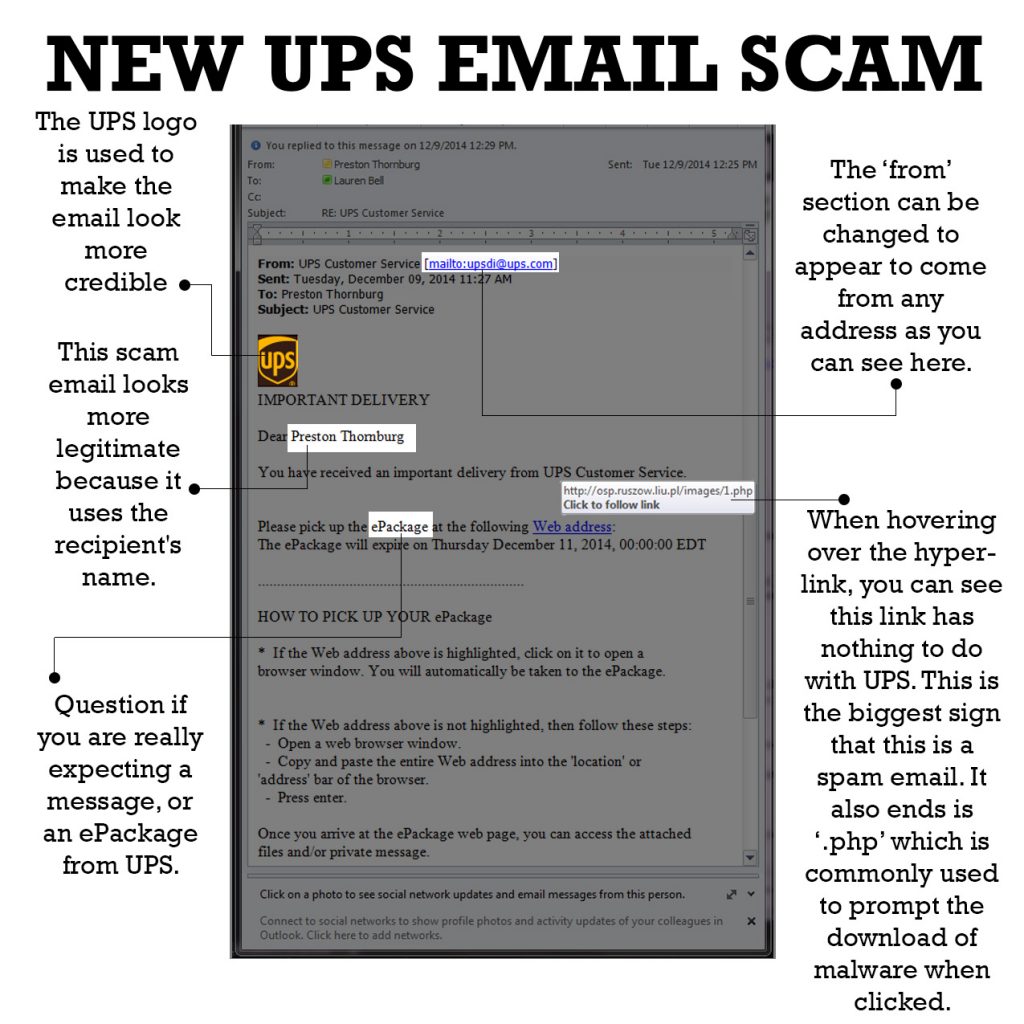
We received this email and quickly realized it was not truly from UPS. Though the senders attempt to make it look legitimate through the use of the UPS logo and other tactics, the email simply looks unofficial and at glance, you can see the formatting looks ‘off.’ There are other red flags that show this email is not from UPS.
The ‘from’ section does say that the email is from UPS and displays the address ‘[email protected].’ Generally, the ‘from’ is a good sign that an email is a scam, but in this case, the crooks that composed this email cleverly changed the ‘from’ field.
The link to the supposed ePackage does not direct traffic to UPS.com. Instead, it shows a link that ends in .php- a type of web code commonly used to deploy malware. You can see where links will lead just by hovering over it with your pointer. Once the link is clicked, malware begins to install on the computer.
To make the email appear more authentic, the crooks used the actual receipt’s name, in this case, Vice President, Preston Thornburg. Though we are unsure exactly how they were able to do this, it does make the email more convincing. The small sign in this section in the email is missing punctuation after “Thornburg.” A true UPS email would have numerous editors look over the email before sending, and a comma would not be missing here.
Lastly, the content and purpose of the email alone should raise questions. Before opening and clicking within emails such as this ask yourself these questions:
- Do I have an account with this company?
- How would this company have obtained my email address?
- Did I ever provide my email address?
- What is the intent of this email?
In the case of this specific email, why would UPS send you an ePackage?
Taking a few moments to ask yourself these questions can prevent a malware infection. It is important to note that email filters cannot catch every spam and malware containing email. Cyber crooks find new ways to bypass these filters as they have done with this email.