Update: Cryptolocker has been stopped by the FBI. A copy-cat infection, Crytptowall, has since surfaced. Read more here.
This ‘CryptoLocker’ virus first made its rounds in January of 2013. Now a new and more aggressive variation of the virus is circulating and demanding $300 to unlock your computer and files. We are asking everyone to practice caution with internet browsing and opening emails as this virus has already infected two of our customers and has been difficult to remove. Because the virus is new, anti-virus software is not able to detect and quarantine the infection yet.
An entire network can be affected by this virus if the original infected computer is on a shared network.
Where does it come from?
So far, our technicians and engineers believe that the virus is acquired through email attachments. It is important to be wary of suspicious emails and delete them immediately. Cyber criminals have become more sophisticated and have the ability to make emails appear credible. For instance, they often use large names like the Better Business Bureau and UPS to trick people into opening emails. If you are not familiar with the sender or receive information that you did not request, delete the email.
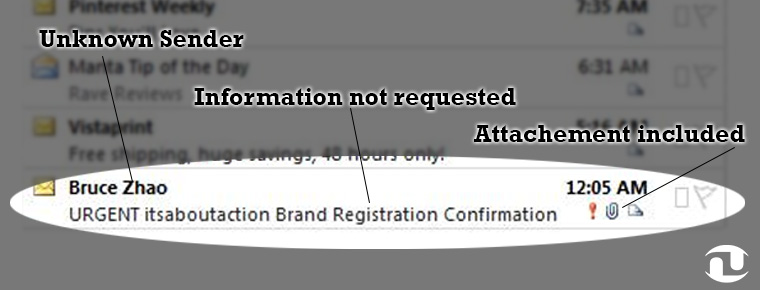
** This is not an actual email that the virus originated from, this is just an example of a suspicious email.
What does it do?
Once a computer is infected, the virus encrypts Microsoft files such as Word, Outlook, Excel, and PowerPoint to a point that they cannot be opened and used. IT professionals nationwide are reporting extreme difficulty in restoring the files if there are no backups in place. We are stressing the importance of backing up files because of this difficulty. It has been reported that the servers that provide the key to unlock the computers are now shut down- making unlocking files impossible. If a computer is on a shared network, even if some users are safe, they can become infected through another computer on the network. Again, we are stressing the importance of backups to prevent catastrophic data loss.
It is likely that many files will not be able to be restored if users do not have backups.
Users then receive a message on their screen the demands $300 for the key to unlocking the encrypted files.

What should infected users do?
People should not give credit card information under any circumstances whatsoever. After-all the criminals are malicious enough to create the malware and cannot be trusted to uphold their end of the deal and unlock the computer and files. If users provide money, the criminals cannot be trusted to only take the demanded $300.00.
Additionally, Microsoft reports on their website that the crooks can not be trusted to restore the files once the money has been paid. If not removed professionally, the virus can remain on the computer and gather information from your computer and jeopardize your security and identity. This virus needs to be removed professionally.



